March 21, 2026
In this article, I reverse engineered a Lua script for the first time and had to learn the Lua language from scratch to reverse this heavily obfuscated script. The process was grueling but learned a lot during the analysis. My primary focus was on deobfuscating the Lua payload to extract the embedded/obfuscated C2 (command-and-control) logic and associated Indicators of Compromise.
Threat actors are actively targeting public GitHub repositories that share tools such as game cheats, Claude code splitters, AI-powered security camera utilities, Amazon validators, coding extensions, and similar software.
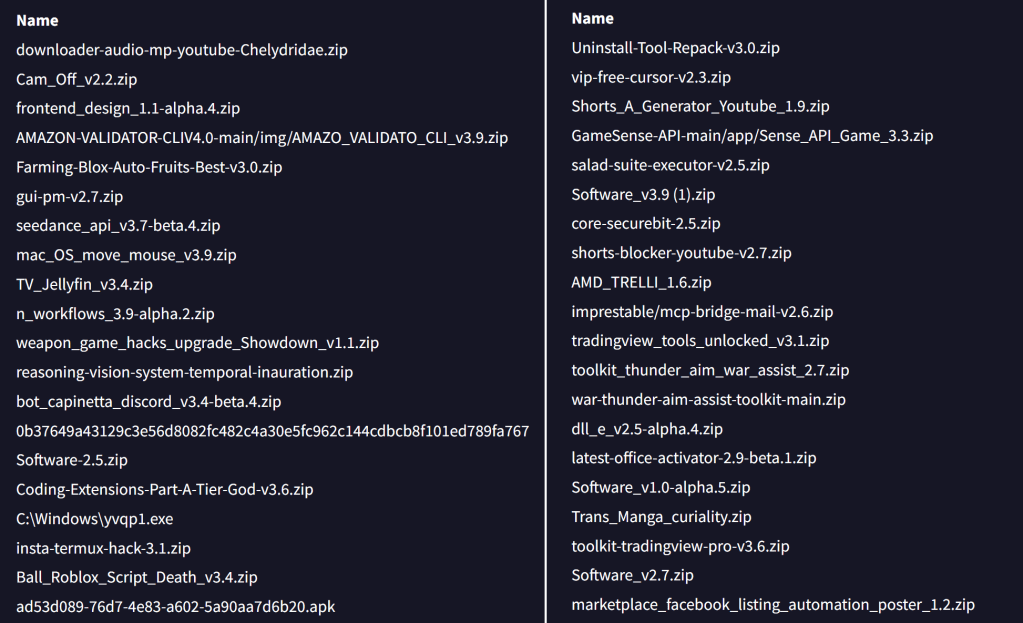
Attackers fork or clone legitimate repositories, then upload a malicious SmartLoader payload into them. When unsuspecting users download and run the software from these compromised repositories, they unknowingly retrieve and execute the malicious Lua payload alongside the intended files.
This campaign remains highly active and continues to evolve, with attackers using GitHub’s trusted platform to distribute the Stealc Infostealer.
Introduction: EtherHiding Technique – Using Blockchain as a Stealthy C2
EtherHiding is an advanced evasion and delivery technique in which attackers leverage blockchain networks as an intermediary infrastructure to host and retrieve command-and-control (C2) information and payload locations.
Instead of hardcoding C2 servers or download URLs directly into malware, threat actors embed or reference this critical data inside smart contracts deployed on the blockchain infrastructure.
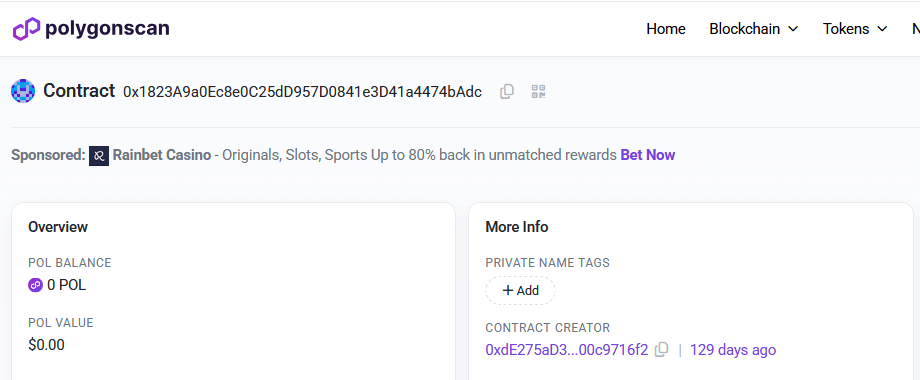
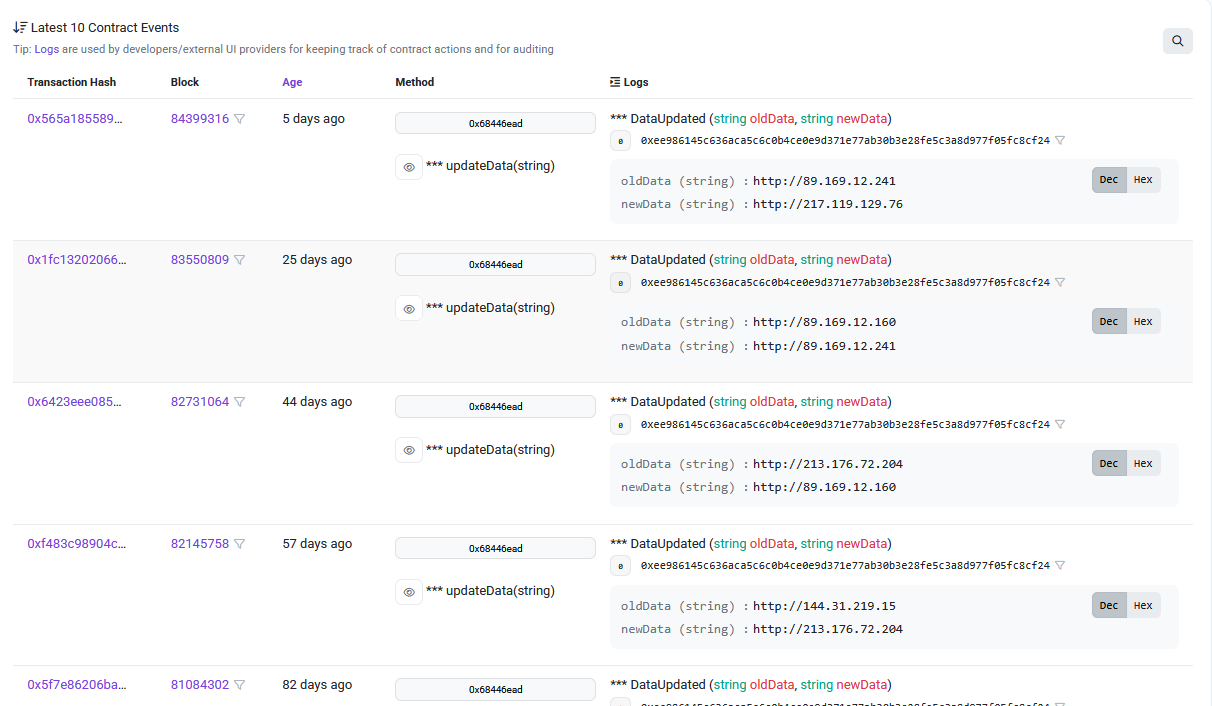
The threat actors are actively leveraging the Polygon Proof-of-Stake (PoS) blockchain to store and manage their command-and-control (C2) server information. By examining the relevant smart contract on a Polygon blockchain explorer (such as PolygonScan), we observe that the attackers frequently create new transactions to update the stored C2 data.
Below is a review of the most recent transaction, created just a few days ago, along with the latest retrieved C2 server IP address.
Attack Flow
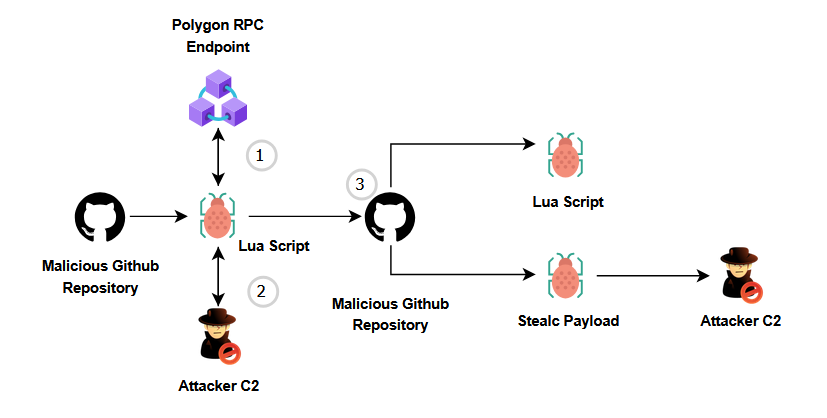
The user downloads a ZIP file from the malicious GitHub repository.
1. The Lua script executes and connects to a Polygon RPC endpoint (leveraging the blockchain network for C2 retrieval).
2. It fetches the next-stage C2 server details from the Polygon RPC endpoint and sends screenshot to Attacker C2
3. The attacker then delivers a second payload, after which the Lua script uses the received data to connect to another attacker-controlled GitHub repository and download the final payloads(Stealc Infostealer).
Technical Analysis
Initial Delivery
Threat actors frequently duplicate legitimate public GitHub repositories and create their own malicious forks or clones to distribute malware while maintaining the appearance of trustworthiness.
In this observed case, attackers duplicated the following legitimate repository (Security-Camera-w-AI), which is designed to provide an AI-powered home security CCTV system.
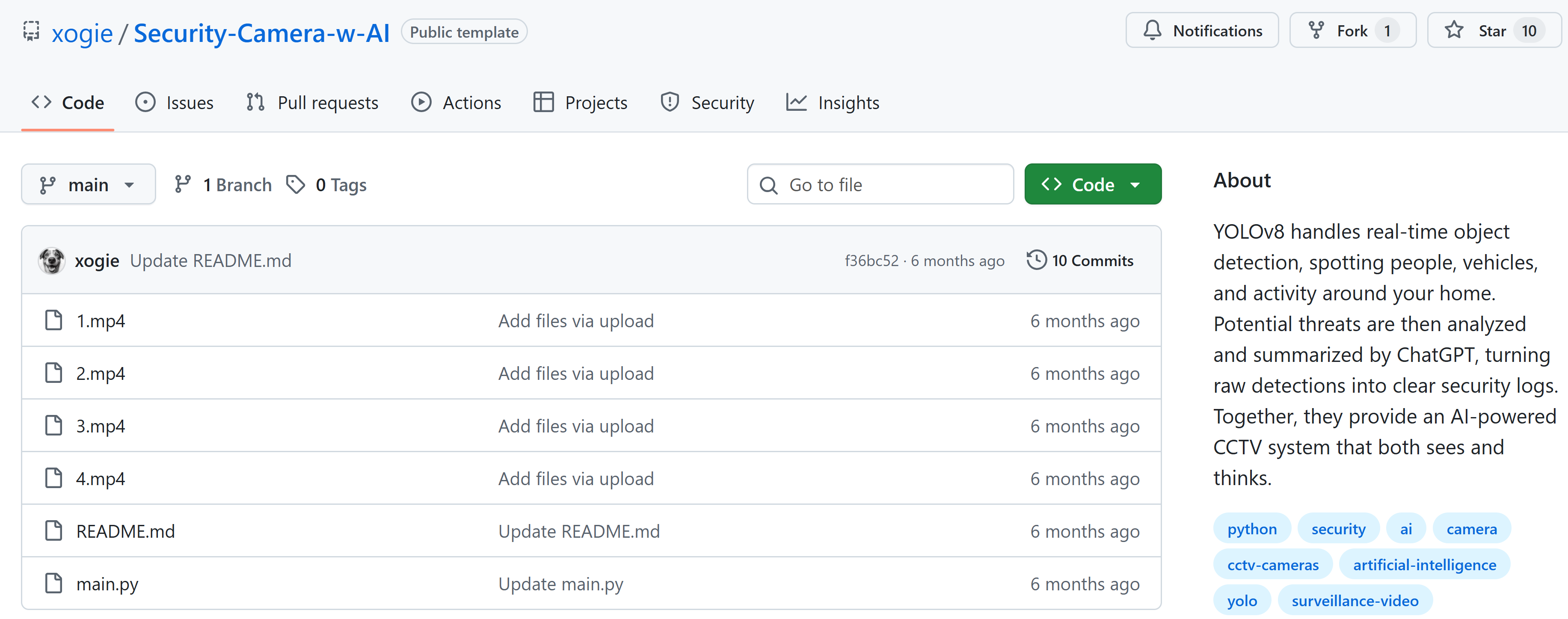
The malicious version of the repository includes an additional suspicious folder named ungodlike. This folder contains a ZIP archive which contains the malicious payload.
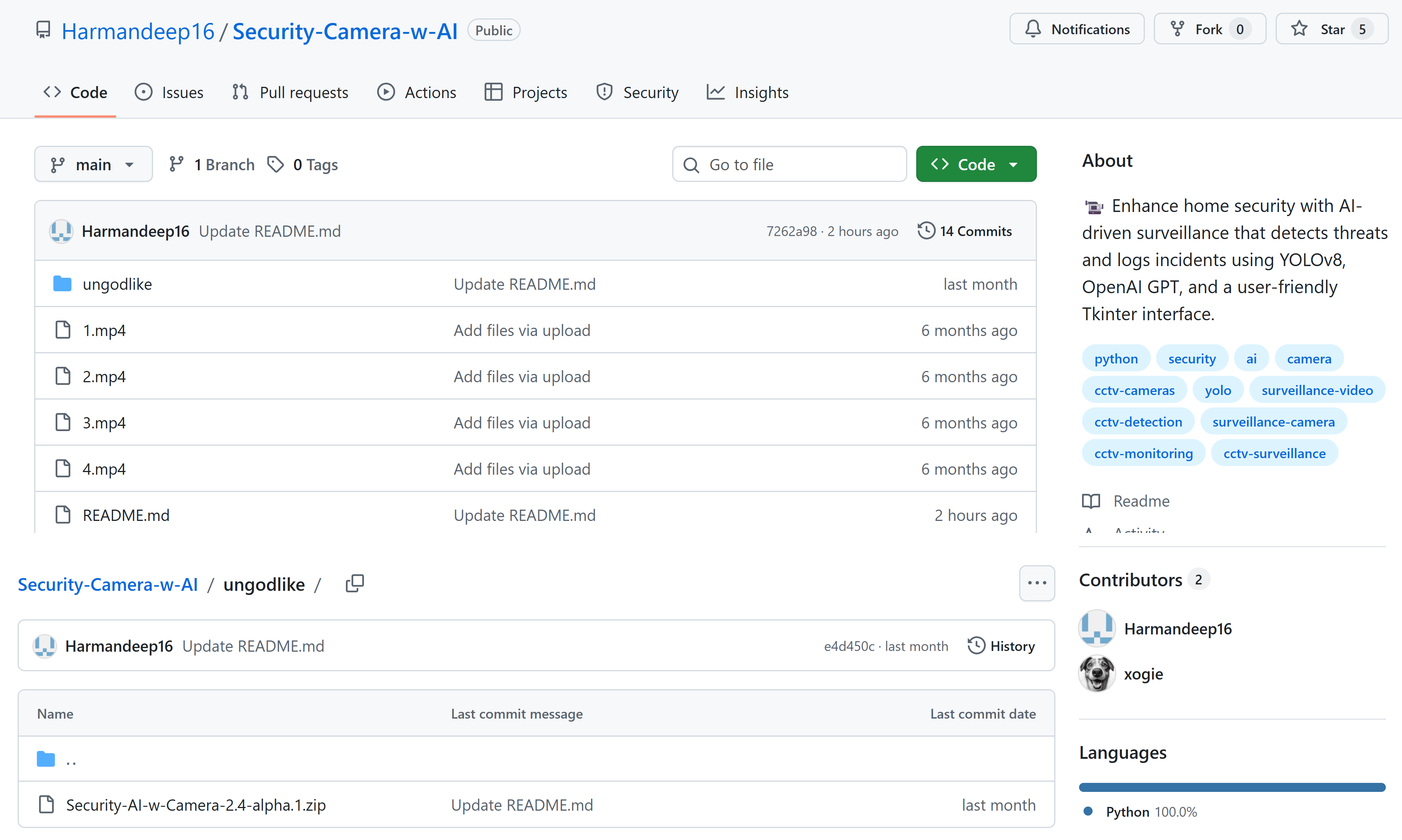
The ZIP file contains the following files:
- Luajit.exe – is the primary standalone executable for the LuaJIT (Just-In-Time) compiler on Windows.
- Uix.txt – Malicious obfuscated Lua script
- Lua51.dll – is a dynamic link library file essential for running programs that use Lua version 5.1
- Launcher.cmd – Command shell script file with command to execute the malicious Lua script using Luajit.exe
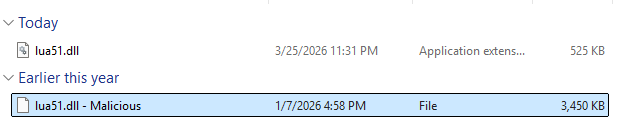
Lua51.dll
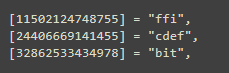
In the analyzed malicious package, the file lua51.dll is a trojanized version of the legitimate Lua 5.1 runtime library, commonly used with LuaJIT for script execution. The file size of the malicious lua51.dll is noticeably larger than legitimate versions. The malicious DLL exports additional functions, particularly those tied to LuaJIT’s FFI (Foreign Function Interface) module to invoke the core Lua C API functions.
Smartloader Lua Script Analysis
The Lua script is heavily obfuscated, and was obfuscated using the Prometheus Lua obfuscator. I examined two variants of the obfuscated script.
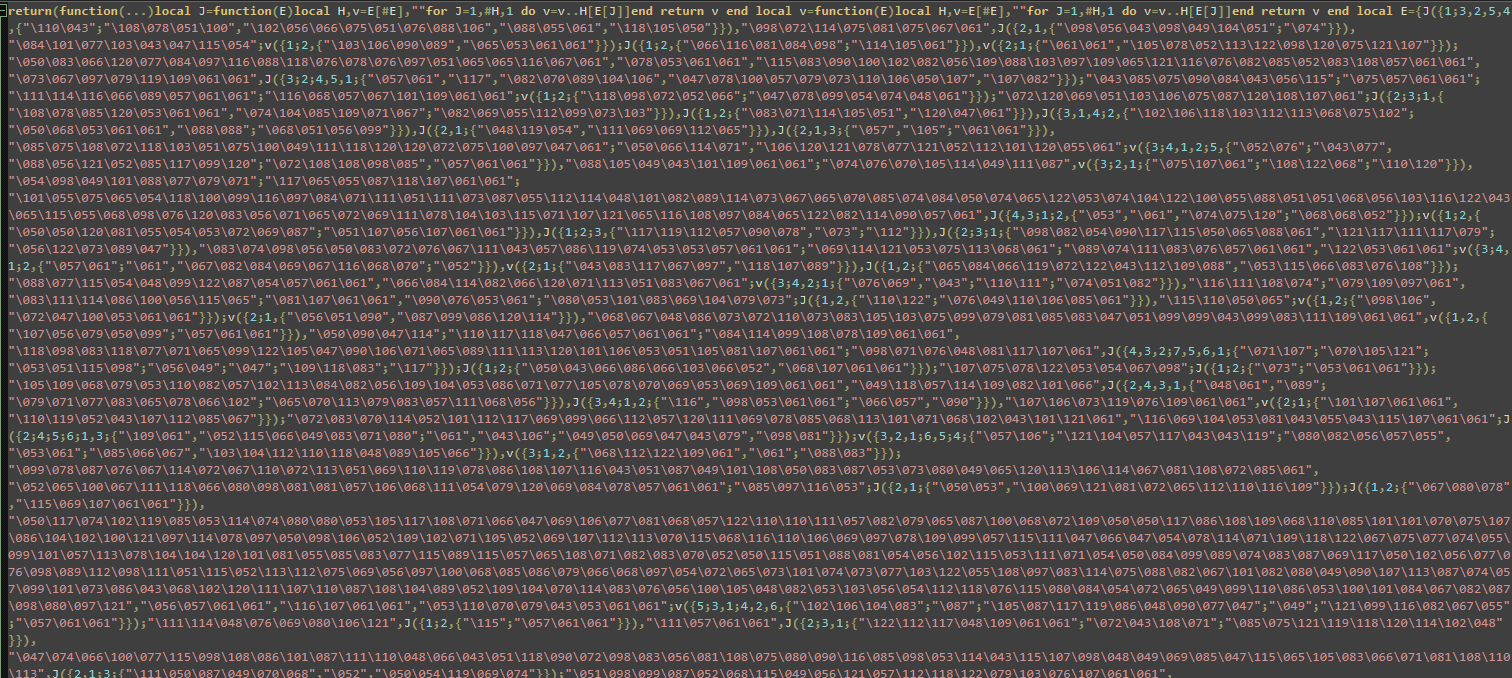
Variant 1: Payload(decimal) → Base64 intermediate → standard string handling; single/default Polygon RPC.
Variant 2: Payload(decimal) → Windows-1252 byte-to-string conversion; multiple Polygon RPC endpoints for improved C2 retrieval reliability.
Due to the extreme complexity of the obfuscation layers, standard Lua IDEs freeze or crash when attempting to load or execute the script directly.
After successfully deobfuscating the initial script, several sophisticated anti-debugging and anti-tampering mechanisms became clearly visible.
- Use of newproxy() to create proxy objects for hidden metatable manipulation.
- Extensive getmetatable() / setmetatable() calls to protect critical tables by locking their metamethods.
- Loading of the global environment using getfenv() into custom tables
Even after initial deobfuscation, Prometheus’s built-in AntiTamper protection detects when obfuscated code is being altered, analyzed, or debugged. If tampering is detected, execution halts with a warning: “Tamper Detected”.
To continue analysis, I manually reversed and patched the script:
- Modified control-flow paths
- Altered conditional branches and error-throwing logic
This patching enabled me to trace the actual malicious logic and understand the overall flow.
Script Functionality
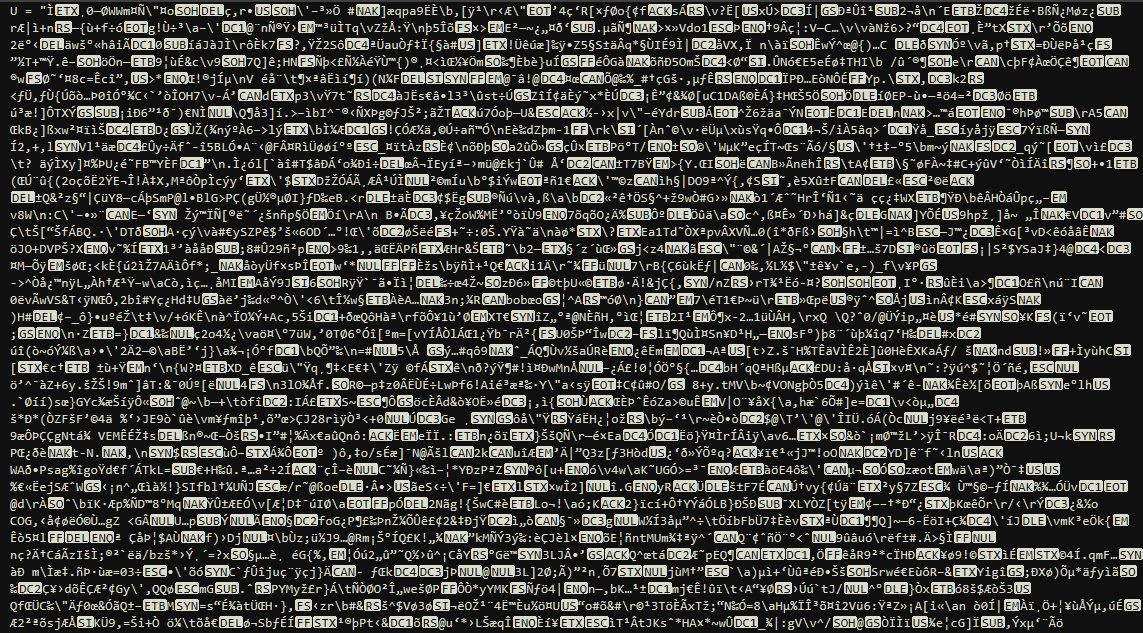
The deobfuscated (and patched) script leverages LuaJIT’s FFI (Foreign Function Interface) module extensively. FFI enables the pure-Lua code to call external C functions and manipulate C data structures without native extensions.
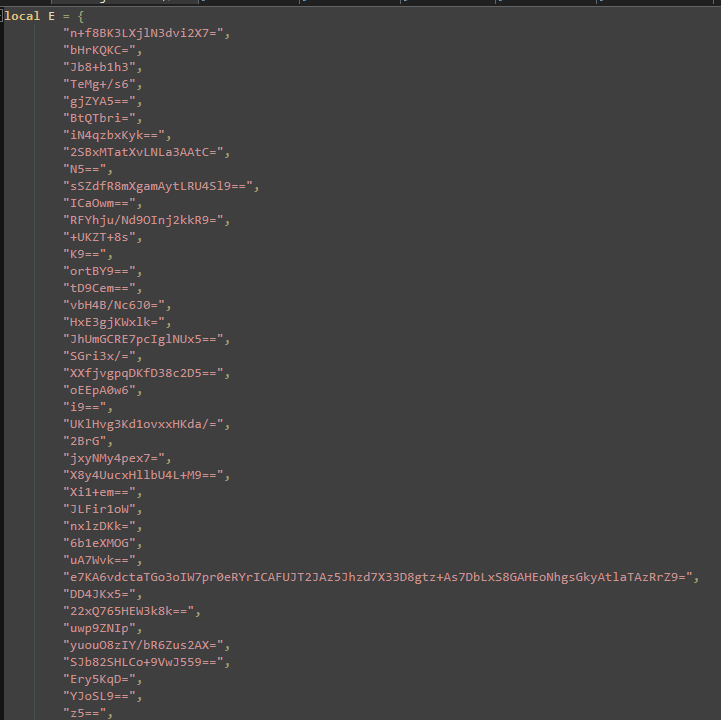
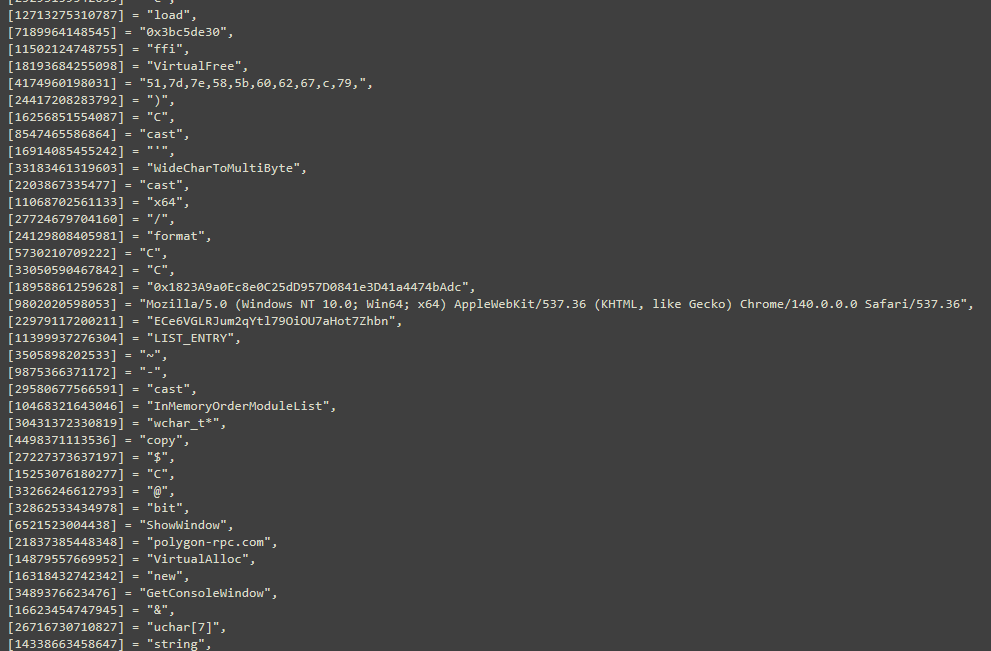
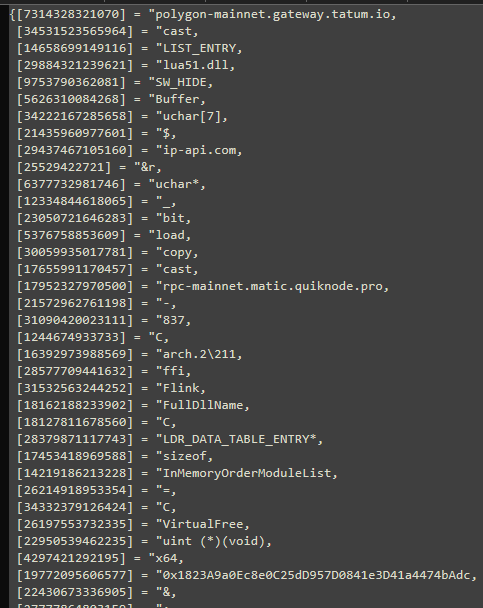
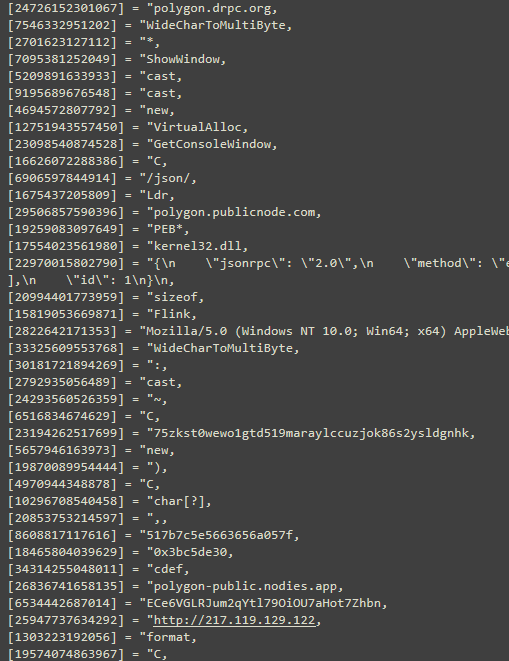
The script establishes a connection to the attacker’s C2 domain. All key Indicators of Compromise (IOCs), including C2 URLs, XOR keys, download paths, and Polygon RPC addresses are stored in obfuscated Lua tables within the script.
In the following section, we will examine the specific C functions recovered from the Lua script, including their purposes in persistence, payload retrieval, and data exfiltration (leading to StealC deployment).
Extracted Script
C functions:
The code contains Struct definitions for the following:
– IMAGE_DOS_HEADER, IMAGE_DATA_DIRECTORY, IMAGE_FILE_HEADER, IMAGE_OPTIONAL_HEADER32, IMAGE_NT_HEADERS32, IMAGE_OPTIONAL_HEADER64, IMAGE_NT_HEADERS64, IMAGE_EXPORT_DIRECTORY, LIST_ENTRY, PEB_LDR_DATA, PEB, UNICODE_STRING, LDR_DATA_TABLE_ENTRY, BITMAPINFOHEADER, BITMAPFILEHEADER, BITMAP, RGBQUAD, BITMAPINFO, OSVERSIONINFOEXW, TOKEN_ELEVATION
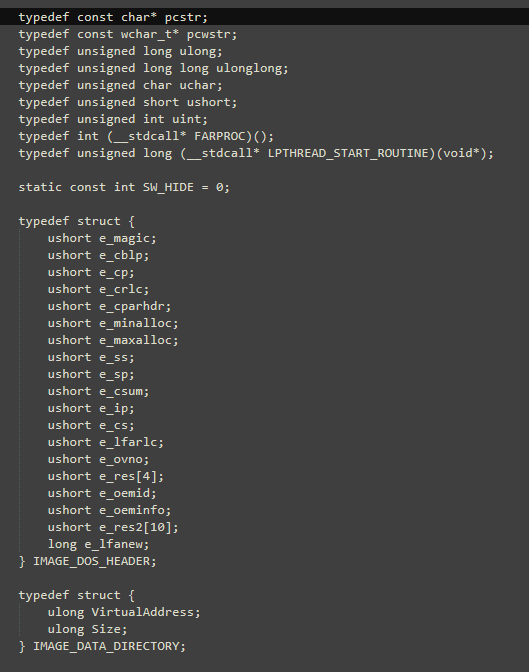
The script calls the following Windows API functions to capture a screenshot of the victim’s machine.
API calls
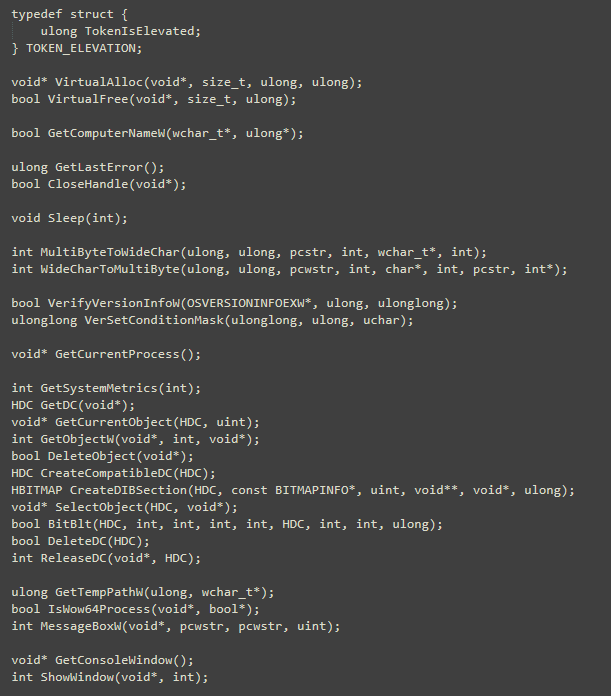
The script also loads more API in a different table that will later be used to connect to blockchain domain and to retrieve the payload from there. Based on the observed Windows API calls, the infection chain progresses to full payload installation and persistence on the victim machine as follows:
- The script downloads the final-stage payload
- After successful download, the payload binary is written to disk.
- One or more directories are created on the local filesystem
- Registry keys are modified to establish persistence.
Extracted IOC
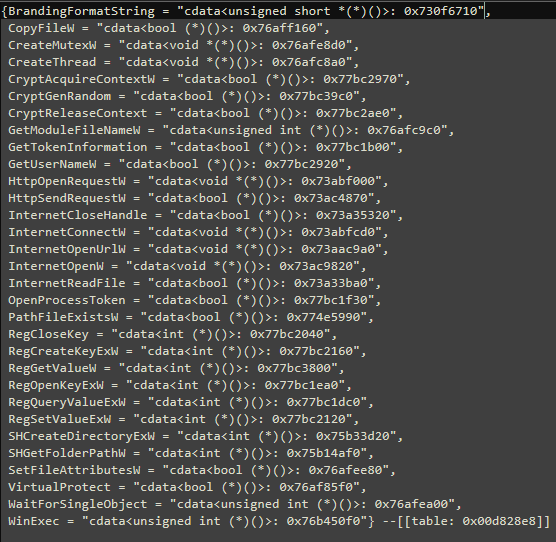
The script finally extracts the base64 payload to a table. The script also populates an additional table with the strings required to execute the C code.
Program Flow
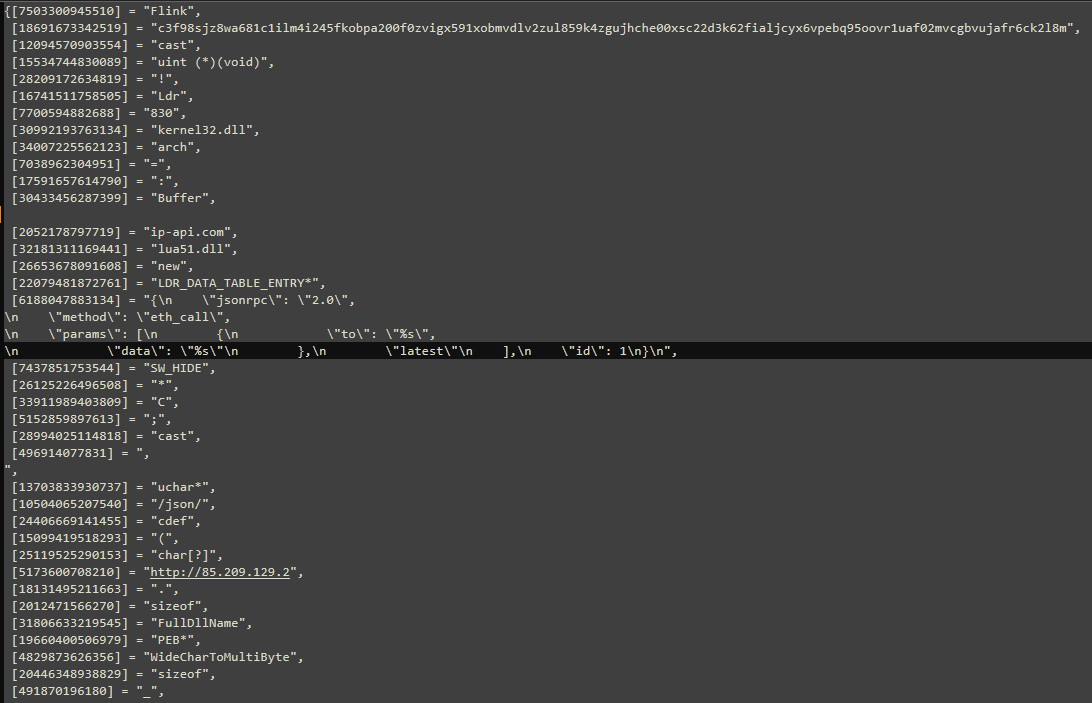
The script dynamically loads multiple additional DLLs using ldrloaddll. The malware creates a mutex with the following long hardcoded name:
c3f98sjz8wa681c1ilm4i245fkobpa200f0zvigx591xobmvdlv2zul859k4zgujhche00xsc22d3k62fialjcyx6vpebq95oovr1uaf02mvcgbvujafr6ck2l8m
This mutex prevents multiple instances of the payload from running simultaneously on the same machine.
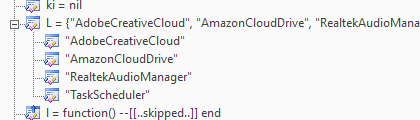
The script enumerates the following user-specific directories:
- C:\Users\BBBB\AppData\Local\Temp\
- C:\Users\BBBB\AppData\Roaming\
- C:\Users\BBBB\Desktop\
Scheduled Tasks: The script also creates schedules task under the following names for persistence. These tasks are configured to execute the malicious Lua script daily at a predetermined time.
Internet Connectivity and Geolocation Check
The payload performs connectivity and geolocation checks before proceeding to C2 communication:
- Sends a GET request to ip-api[.]com/json with a custom User-Agent string.
- Parses the JSON response to obtain the victim’s approximate geolocation
- If ip-api.com fails to return valid data, the malware falls back to a basic internet connectivity test:
- Attempts to connect to https://www.microsoft.com.
- If this also fails, the payload enters a sleep loop periodically reattempts until connectivity is confirmed.
Polygon Blockchain Contract Query for Dynamic C2 Once internet connectivity and geolocation data are successfully retrieved:
- The payload constructs and sends a POST request to a Polygon blockchain RPC endpoint (polygon-rpc.com).
- The request targets a specific smart contract address (0x1823A9a0Ec8e0C25dD957D0841e3D41a4474bAdc).
- The JSON payload sent to the contract typically includes:
{\n \"jsonrpc\": \"2.0\",\n \"method\": \"eth_call\",\n \"params\": [\n {\n \"to\": \"%s\",\n \"data\": \"%s\"\n },\n \"latest\"\n ],\n \"id\": 1\n}\n
The smart contract processes the request and returns the current active C2 domain.
After successfully querying the Polygon blockchain smart contract , the Lua script receives the active C2 domain information).
The script then:
- Grabs a screenshot of the victims machine and sends an HTTP POST request to the retrieved C2 server.
- The C2 server responds with the necessary information to fetch the final payload(s).
Based on the server’s response, the Lua script proceeds to download the next-stage payload directly from GitHub. In this campaign, the attacker-controlled GitHub repository hosts two XOR encoded distinct payloads:
- Next stage Lua script
- StealC InfoStelaer payload
Both the payloads are obfuscated using XOR key(ECe6VGLRJum2qYtl79OiOU7aHot7Zhbn) and can be decrypted using the key. (Note: The XOR key is present in the string table extracted from the Lua script, as mentioned above.)
Final Payload
Next Stage Lua Script
The second analyzed Lua script variant also begins with sequences of decimal-encoded payload . However, after deobfuscation, these decimal bytes are interpreted and decoded differently. The decimal values are converted into byte sequences that represent string characters using the Windows-1252 (CP1252) character encoding set. After correcting the encoding and patching remaining tamper/anti-debug checks, the following key IOCs were recovered from the second script variant:
The script contains multiple hardcoded Polygon RPC endpoint domains.
StealC InfoStealer Payload
The final payload is the Stealc infostealer malware, The Infostealer attempts to steal Browser Credential, browser cookies, Cryptocurrency Wallet and Email Client and Account Data. The data is then exfiltrated to attacker C2 server(213.176.72[.]200).
IOC’s (Partial List)
89.169.12[.]241
217.119.129[.]76
89.169.12[.]160
85.209.129[.]2
https://github.com/Harmandeep16/Security-Camera-w-AI
http://213.176.72%5B.%5D200/3d9c1a1d0dc9436eb7b7%5B.%5Dphp
https://github.com/HHNiPA/AMAZON-VALIDATOR-CLIV4.0
https://github.com/hellodrcodex/jvg/tree/main/88
http://github.com/sameer2135/OffCam/raw/refs/heads/main/opinable/Cam_Off_v2.2.zip
https://github.com/hari11v/20-God-Tier-AI-Coding-Extensions-Part-1/raw/refs/heads/main/discipular/Coding-Extensions-Part-A-Tier-God-v3.6.zip/